Transcription from a lecture by Raz Mesinai, “The waveform is a veil”
“Don’t make a sound”…
Ironically, one of the most effective ways to sneak into a computer system is by making a sound. Reports of hackers using malicious code woven into ordinary audio Wav. Files containing music for espionage operations, bit coin mining and monetary gain should be of no surprise, since using sound for clandestine operations is as ancient as the tools themselves, from the drum being used for communicating over farther distances than the voice could carry or the eye could see, to the Ghost Army during WW2 using turntables to playback sound effects to deflect the enemy, to Leon Theremin developing surveillance equipment for Russia, the inspiration for practically every invention we use for producing music has roots in espionage and the act of communicating secrets.
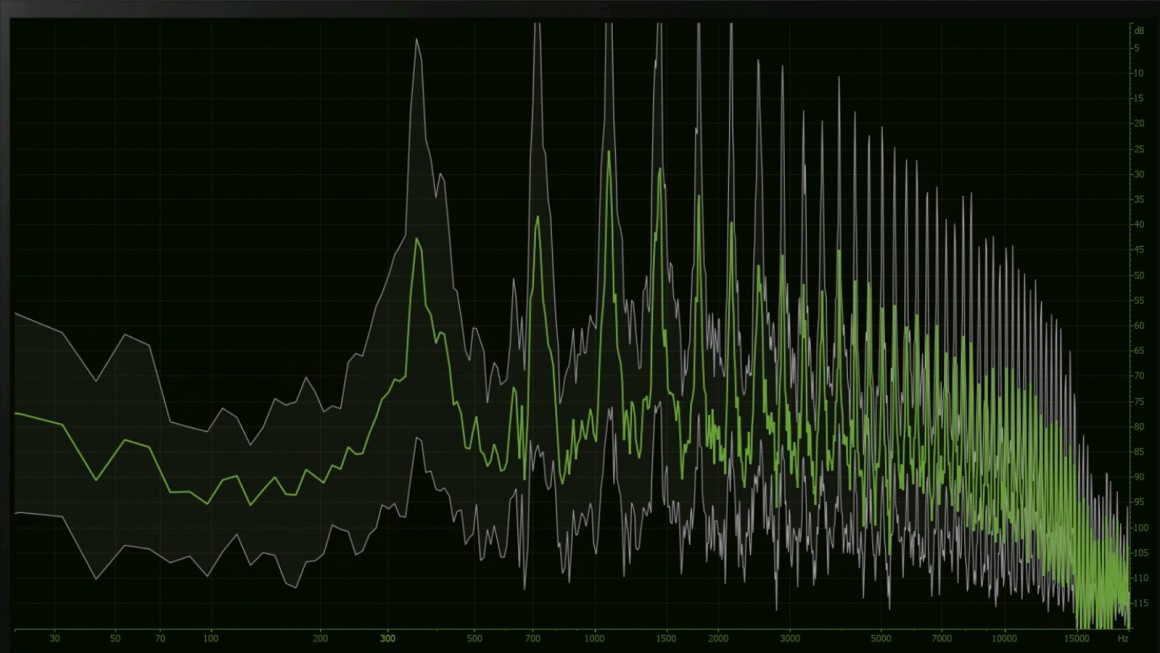
While teaching at UCSD I came across covert acoustical mesh networks, a decentralized communication system that transmits data by using sound to connect computers through the air, utilizing just the microphones and speakers as entrance points for all kinds of mischief. The article by Michael Hanspach and Michael Goetz (Fraunhofer FKIE, Wachtberg, Germany) “On Covert Acoustical Mesh Networks In Air” proposed the threat of covertly targeting a computer using loud speakers and microphones commonly available on most devices for entertainment, video conferencing, IP phone communications, utilizing inaudible frequencies i.e. the ultrasonic or near ultrasonic frequency range. Based on tech originally made for underwater communication systems, the idea came from presenting proof of concept (POC) trials for acoustical infections as a method of communication between air-gapped computer systems. Air-gapping being a form of securing sensitive data from any hacking possible, revealed this very obvious but not yet noticed loop hole. While any laptop lets you turn off basic radio connections, like WIFI and Bluetooth, the most effective way to air gap a computer was to physically remove all the hardware that allowed access, or to use a computer that did not come with any hardware for it whatsoever, such as an Intel Nuc or Gigabyte Brix, but not many removed the speakers or microphones, leaving them open to an attack from an acoustic mesh network. What stuck out to me was how even now the sound system was the last considered back door when it came to cyber security yet for centuries sound systems and sound itself was exactly the means for some of the greatest ideas for infiltration. Through studying the use (or misuse depending on the user or users) of tools from the past, present and future for distributing sound across various dimensions, including sound systems, bodies, cultures and economies, we can better understand and develop beyond what music was speculated to be, and once we become unbound from the narrative that music’s purpose is solely for entertainment and refocus on it as a tool for communication, most of the issues surrounding economics and ownership become less shrouded in mystery.
Guglielmo Marconi, a central figure in the modern understanding of communication and the idea of globally networked wireless communications who improved upon wireless Morse Code telegraphy by developing a more practical method using radio waves, also paved the way for RCA leader (and soundboy #1) David Sarnoff who was the cause of holding back FM radio from coming to existence for decades, leaving us with only AM to work with so that only the few ruling corporations could thrive. In 1903, Marconi met his match (or at least close) and was soundboy’d by British inventor, magician and manager of the Anglo-American Telegraph Company Nevil Maskelyne whom vandalized a presentation of Marconi’s invention by intercepting a Morse Code message meant to play to an audience using a 50-meter radio mast. Maskelyne interrupted Marconi’s message with a barrage of insults to show that it was flawed, making it possibly one of the first known examples of “Grey Hat” hacking not to mention a classic case of corporate espionage. Maskelyne’s approach was to disavow the idea that Marconi had a chance whatsoever in creating a secure connection to remove any hope in security. Maskelyne was both wrong and right, in that we did eventually use Marconi’s inventions yet also have been constantly proven that security will always be an issue, and security is at the crux of what determines ownership, because ownership is based on secrecy as our property must be kept secure for it to be truly owned by us. The physicality of the object determines whether we feel, emotionally, that something is in fact our property.
We artists feel as though we are using these devices for communicating voices of resistance, but that is compromised when we are not aware of the history of our weapons or what we are actually fighting for. Electronic musicians are usually dismayed by the unavoidable approach of artificial intelligence-based music productions, yet unknowingly give the data needed to develop the AI away, for free, to music platforms making millions. As opposed to these hackers, when we produce secrecy is less useful, as art is meant to be popular and artists wish for their work to be exposed… when we drop an album, we want that to be known. The danger here is in us becoming advert to the idea of ownership while still needing property, as we do not truly own our audio files anyway, it is like owning air, and god forbid we do that.
This “feeling” of ownership is the alchemy behind the success of another waveform gangster, Steve Jobs, who said “I believe that the same spirit that causes people to want to be poets instead of bankers can be put into products, and those products can be manufactured and given to people, and they can sense that spirit.” What Steve Jobs wanted to do was to give that indescribable feeling one got when opening a vinyl record, but unlike the future artists who came to be dependent on his products, he knew how to create objects and value, and the convergence of these elements I am ranting about here can be seen within the law suit which came about between Apple Computers and The Beatles owned company Apple Corp. In September of 2003 a revisiting of the litigation which begun decades before between Apple computers and Apple Corps, a company owned by The Beatles and their families, was renewed upon the creation of I-Tunes. As in 1989 Apple Computers and Apple Corps settled their dispute over the ownership of the name “Apple”, where Apple Corps agreed to allow Apple Computers to use the name Apple and its logo, as long as Apple Computers remained outside of the music industry, which was clearly violated as soon as Apple Computers launched I-Tunes, which not only breached the agreement of staying out of the music industry, but in fact took it over. Jobs’s approach was to simply do something he agreed not to do and to then pretend that it was never a problem to begin with, and then to deal with the aftermath with the weapons he accumulated from his innovations, namely wealth using time that he could buy through lawyer-ing up, a privilege afforded to him by the act of innovating within a copy of a copy of a copy.
With the slightest bit of creative thinking however we can use the same tactics used by these waveform hijackers to gain control over our work and establish additional value to it. What these cyber criminals are doing is, in many ways, exactly what musicians and producers should be doing with their audio files, except perhaps without all of the sexy illegal activity. Am I recommending that music productions also pose as malware? No, but it is an example of utilizing every bit of what our music is contained in, as well as a tool that we can claim ownership of.
Links:
Cylance on malware in audio files
On Covert Acoustical Mesh Networks in Air
In Praise Of Copying – Marcus Boon


Leave a reply